Springboot Upload File to Different S3 Buckets
In spider web and mobile applications, it's mutual to provide users with the ability to upload data. Your application may allow users to upload PDFs and documents, or media such equally photos or videos. Every mod web server technology has mechanisms to allow this functionality. Typically, in the server-based environment, the process follows this flow:
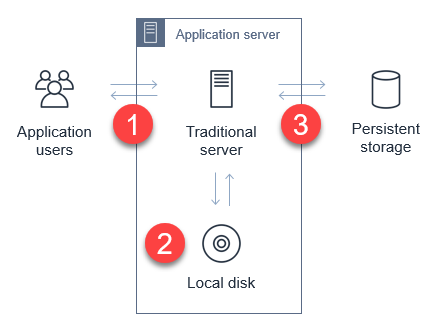
- The user uploads the file to the application server.
- The application server saves the upload to a temporary space for processing.
- The awarding transfers the file to a database, file server, or object shop for persistent storage.
While the process is uncomplicated, information technology tin have significant side-furnishings on the functioning of the web-server in busier applications. Media uploads are typically large, so transferring these tin represent a big share of network I/O and server CPU time. You must too manage the country of the transfer to ensure that the entire object is successfully uploaded, and manage retries and errors.
This is challenging for applications with spiky traffic patterns. For example, in a spider web application that specializes in sending vacation greetings, it may experience near traffic only around holidays. If thousands of users attempt to upload media around the same time, this requires you to scale out the application server and ensure that there is sufficient network bandwidth available.
By directly uploading these files to Amazon S3, yous can avoid proxying these requests through your awarding server. This can significantly reduce network traffic and server CPU usage, and enable your application server to handle other requests during busy periods. S3 also is highly available and durable, making it an ideal persistent store for user uploads.
In this blog post, I walk through how to implement serverless uploads and show the benefits of this approach. This pattern is used in the Happy Path web application. You can download the code from this web log mail in this GitHub repo.
Overview of serverless uploading to S3
When you upload direct to an S3 bucket, you must kickoff request a signed URL from the Amazon S3 service. You lot tin and so upload directly using the signed URL. This is 2-step process for your application front stop:

- Call an Amazon API Gateway endpoint, which invokes the getSignedURL Lambda function. This gets a signed URL from the S3 saucepan.
- Directly upload the file from the application to the S3 saucepan.
To deploy the S3 uploader case in your AWS account:
- Navigate to the S3 uploader repo and install the prerequisites listed in the README.dr..
- In a final window, run:
git clone https://github.com/aws-samples/amazon-s3-presigned-urls-aws-sam
cd amazon-s3-presigned-urls-aws-sam
sam deploy --guided
- At the prompts, enter s3uploader for Stack Proper name and select your preferred Region. Once the deployment is complete, note the APIendpoint output.The API endpoint value is the base URL. The upload URL is the API endpoint with
/uploadsappended. For example:https://ab123345677.execute-api.united states-west-two.amazonaws.com/uploads.

Testing the application
I show 2 ways to test this application. The first is with Postman, which allows you to directly call the API and upload a binary file with the signed URL. The second is with a basic frontend application that demonstrates how to integrate the API.
To test using Postman:
- First, copy the API endpoint from the output of the deployment.
- In the Postman interface, paste the API endpoint into the box labeled Enter request URL.
- Cull Ship.

- Afterwards the asking is complete, the Body department shows a JSON response. The uploadURL attribute contains the signed URL. Copy this attribute to the clipboard.
- Select the + icon side by side to the tabs to create a new request.
- Using the dropdown, change the method from GET to PUT. Paste the URL into the Enter request URL box.
- Cull the Body tab, and so the binary radio button.

- Choose Select file and choose a JPG file to upload.
Cull Transport. You see a 200 OK response afterward the file is uploaded.
- Navigate to the S3 console, and open up the S3 bucket created by the deployment. In the bucket, you see the JPG file uploaded via Postman.

To test with the sample frontend awarding:
- Re-create index.html from the example's repo to an S3 bucket.
- Update the object's permissions to make information technology publicly readable.
- In a browser, navigate to the public URL of index.html file.

- Select Cull file then select a JPG file to upload in the file picker. Choose Upload image. When the upload completes, a confirmation message is displayed.
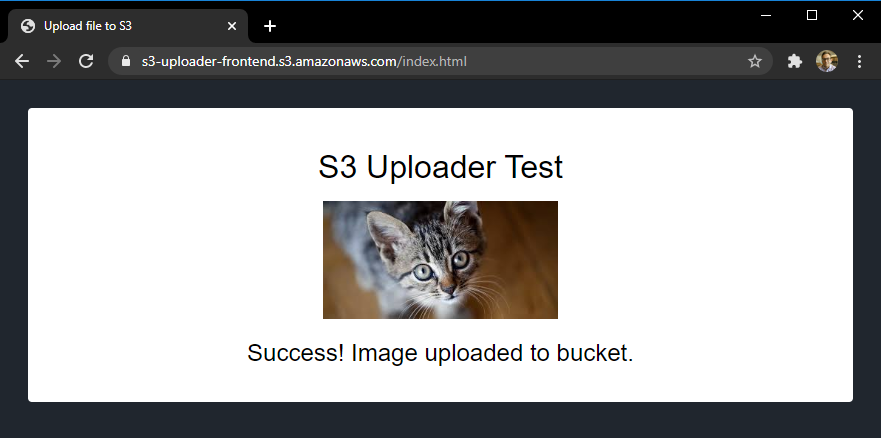
- Navigate to the S3 console, and open the S3 saucepan created by the deployment. In the bucket, you run across the second JPG file you uploaded from the browser.

Understanding the S3 uploading process
When uploading objects to S3 from a web awarding, yous must configure S3 for Cross-Origin Resource Sharing (CORS). CORS rules are divers equally an XML certificate on the bucket. Using AWS SAM, you tin can configure CORS as part of the resource definition in the AWS SAM template:
S3UploadBucket: Type: AWS::S3::Bucket Backdrop: CorsConfiguration: CorsRules: - AllowedHeaders: - "*" AllowedMethods: - Go - PUT - HEAD AllowedOrigins: - "*" The preceding policy allows all headers and origins – it'southward recommended that you use a more restrictive policy for production workloads.
In the first step of the process, the API endpoint invokes the Lambda function to brand the signed URL request. The Lambda function contains the post-obit lawmaking:
const AWS = require('aws-sdk') AWS.config.update({ region: process.env.AWS_REGION }) const s3 = new AWS.S3() const URL_EXPIRATION_SECONDS = 300 // Main Lambda entry point exports.handler = async (upshot) => { return await getUploadURL(event) } const getUploadURL = async function(issue) { const randomID = parseInt(Math.random() * 10000000) const Central = `${randomID}.jpg` // Get signed URL from S3 const s3Params = { Bucket: process.env.UploadBucket, Central, Expires: URL_EXPIRATION_SECONDS, ContentType: 'prototype/jpeg' } const uploadURL = look s3.getSignedUrlPromise('putObject', s3Params) return JSON.stringify({ uploadURL: uploadURL, Cardinal }) } This function determines the proper name, or primal, of the uploaded object, using a random number. The s3Params object defines the accepted content blazon and also specifies the expiration of the key. In this case, the cardinal is valid for 300 seconds. The signed URL is returned equally office of a JSON object including the key for the calling application.
The signed URL contains a security token with permissions to upload this single object to this bucket. To successfully generate this token, the code calling getSignedUrlPromise must have s3:putObject permissions for the bucket. This Lambda function is granted the S3WritePolicy policy to the bucket by the AWS SAM template.
The uploaded object must lucifer the same file name and content type as divers in the parameters. An object matching the parameters may be uploaded multiple times, providing that the upload procedure starts before the token expires. The default expiration is 15 minutes only yous may want to specify shorter expirations depending upon your use example.
Once the frontend application receives the API endpoint response, information technology has the signed URL. The frontend application then uses the PUT method to upload binary data direct to the signed URL:
let blobData = new Blob([new Uint8Array(assortment)], {type: 'image/jpeg'}) const upshot = await fetch(signedURL, { method: 'PUT', torso: blobData }) At this indicate, the caller application is interacting direct with the S3 service and not with your API endpoint or Lambda part. S3 returns a 200 HTML status lawmaking once the upload is complete.
For applications expecting a large number of user uploads, this provides a simple way to offload a big corporeality of network traffic to S3, away from your backend infrastructure.
Adding hallmark to the upload process
The current API endpoint is open, available to whatsoever service on the cyberspace. This means that anyone can upload a JPG file once they receive the signed URL. In most production systems, developers want to apply authentication to control who has access to the API, and who can upload files to your S3 buckets.
You can restrict access to this API by using an authorizer. This sample uses HTTP APIs, which back up JWT authorizers. This allows you to command access to the API via an identity provider, which could be a service such equally Amazon Cognito or Auth0.
The Happy Path awarding only allows signed-in users to upload files, using Auth0 as the identity provider. The sample repo contains a second AWS SAM template, templateWithAuth.yaml, which shows how you can add an authorizer to the API:
MyApi: Type: AWS::Serverless::HttpApi Properties: Auth: Authorizers: MyAuthorizer: JwtConfiguration: issuer: !Ref Auth0issuer audience: - https://auth0-jwt-authorizer IdentitySource: "$request.header.Authorisation" DefaultAuthorizer: MyAuthorizer Both the issuer and audience attributes are provided by the Auth0 configuration. By specifying this authorizer as the default authorizer, it is used automatically for all routes using this API. Read part 1 of the Ask Effectually Me series to learn more than nearly configuring Auth0 and authorizers with HTTP APIs.
After authentication is added, the calling web application provides a JWT token in the headers of the request:
const response = await axios.get(API_ENDPOINT_URL, { headers: { Say-so: `Bearer ${token}` } }) API Gateway evaluates this token earlier invoking the getUploadURL Lambda part. This ensures that only authenticated users can upload objects to the S3 bucket.
Modifying ACLs and creating publicly readable objects
In the current implementation, the uploaded object is non publicly accessible. To make an uploaded object publicly readable, you must set its access control list (ACL). In that location are preconfigured ACLs available in S3, including a public-read selection, which makes an object readable by anyone on the internet. Fix the appropriate ACL in the params object earlier calling s3.getSignedUrl:
const s3Params = { Bucket: process.env.UploadBucket, Key, Expires: URL_EXPIRATION_SECONDS, ContentType: 'image/jpeg', ACL: 'public-read' } Since the Lambda function must have the appropriate bucket permissions to sign the request, y'all must also ensure that the function has PutObjectAcl permission. In AWS SAM, yous tin can add the permission to the Lambda function with this policy:
- Statement: - Effect: Let Resources: !Sub 'arn:aws:s3:::${S3UploadBucket}/' Activity: - s3:putObjectAcl Decision
Many web and mobile applications allow users to upload data, including big media files similar images and videos. In a traditional server-based application, this can create heavy load on the application server, and also use a considerable amount of network bandwidth.
By enabling users to upload files to Amazon S3, this serverless design moves the network load away from your service. This tin make your application much more scalable, and capable of handling spiky traffic.
This web log post walks through a sample awarding repo and explains the process for retrieving a signed URL from S3. Information technology explains how to the test the URLs in both Postman and in a spider web application. Finally, I explain how to add authentication and make uploaded objects publicly attainable.
To learn more, see this video walkthrough that shows how to upload straight to S3 from a frontend spider web application. For more serverless learning resources, visit https://serverlessland.com.
stoddarddoely1980.blogspot.com
Source: https://aws.amazon.com/blogs/compute/uploading-to-amazon-s3-directly-from-a-web-or-mobile-application/